The IoT Revolution Shaping the Future World
INTRODUCTION
How would the world be without the Internet? It is difficult to imagine such a scenario we have never seen. Today, the internet has become more and more important for everybody in both personal and professional life. The Internet of Things (IoT) refers to the increasing network of physical objects that feature an IP address for Internet connectivity and the communication that occurs between these objects and other Internet-enabled devices and systems. Different devices such as smartphones, sensors, mobile computers, and other smart objects are examples of daily things we deal with. These and other IOT-related technologies significantly affect new ICT and enterprise systems technologies.
History of IoT technologies
When some college students planned to alter a Coca-Cola vending machine to allow for remote monitoring of its contents in the 1980s, the idea of embedding sensors and intelligence into physical things was initially put out. But technology was clunky, and advancement was slow. The term “Internet of Things” was first introduced in 1999 by computer scientist Kevin Ashton. While working at Procter and Gamble, Ashton promoted the use of radio-frequency identification (RFID) chips to track objects as they move through a supply chain.
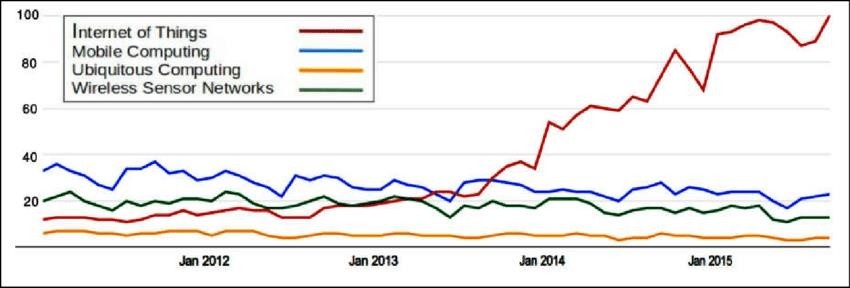
Public interest in IoT technology began to grow as linked devices proliferated on the market throughout the ensuing decade. According to the State of the Connected World report by the World Economic Forum, there are currently more connected devices than people in the world. It is anticipated that by 2025, 41.6 billion devices will be collecting data on how we live, work, move through our cities, and use and maintain the machines on which we rely. The digital revolution that is taking place because of cutting-edge technology like robots, the Internet of Things, and artificial intelligence is referred to as the Fourth Industrial Revolution. These technologies are now used more frequently thanks to COVID-19.
Application of the Internet of Things
Connected Health
- IoT has many uses in the healthcare industry, including advanced & smart sensors, equipment integration, and remote monitoring tools. It can enhance how doctors provide treatment while also keeping patients secure and healthy. IoT in healthcare can enable patients to contact their doctors more frequently, which can increase patient engagement and happiness.
Smart City
- Smart city is a powerful IoT application that is generating interest among all people around the world. Intelligent surveillance, better energy management systems, automated transportation, water distribution, urban security, and environmental monitoring. These are a few examples of Internet of Things applications for smart cities. IoT will deal with major problems that urban residents face, such as pollution, traffic congestion, a shortage of energy supply, etc.
Connected Cars
- With the use of signal phase and timing data, vehicles with IoT capabilities may predict and report traffic patterns. Connected cars can exchange information with one another. Drivers can use less gasoline and drive more safely if they can anticipate traffic.
Smart Home and Farming
- IoT smart products are designed to help monitor homes and crop fields using sensors and automated irrigation systems. As a result, householders’ farmers and associated brands can easily monitor the field and house conditions from anywhere without any hassle.
Potential Risks of the Internet of Things and Solutions
There are many security issues with gadgets that may connect to the internet. The general cybersecurity challenges aren’t new, even though the Internet of Things has connected to new gadgets. If we’ve benefited from the Internet, we’ve had to deal with hackers. A new era of connectedness has arrived thanks to the Internet of Things (IoT), but it also comes with several threats and difficulties. Security is one of the main issues. The potential for cyberattacks is enormous, given the sheer number of networked gadgets gathering and transmitting data. IoT device vulnerabilities can be used by hackers to get unauthorized access to customer data, business networks, or even vital infrastructure, posing a serious risk to privacy and national security.

Data privacy is yet another danger. IoT devices frequently collect enormous volumes of sensitive and personal data, including location-based information and health information. These data can be treated improperly and result in privacy violations and identity theft if they are not adequately protected. Moreover, it might be difficult to maintain compliance with data protection requirements due to the sheer volume of data created by IoT devices, which can overwhelm conventional data management systems. The Internet of Things (IoT) has ushered in a new era of connectivity, but it also brings with it several risks and challenges. One of the key challenges is security. Given the sheer volume of networked devices collecting and transferring data, there is a huge possibility for cyberattacks. Hackers may utilize IoT device vulnerabilities to gain unauthorized access to customer data, company networks, or even critical infrastructure, posing a major risk to privacy and national security. Another risk is data privacy. IoT devices routinely gather massive amounts of private and sensitive data, such as health and location-based data. If these data are not securely protected, they may be handled unlawfully, leading to privacy violations and identity theft. Additionally, the massive volume of data that IoT devices produce.
The Solutions for the risks
Physical security
- Physical security is vital for avoiding unauthorized access to a device because IoT applications are frequently remote. The use of robust components and specialized gear that makes accessing your data more challenging is beneficial in this situation.

Private networks
- Security risks exist even while sending and receiving communications using remotely deployed devices. Using public-access networks, like Wi-Fi, to connect devices and enable communication exposes those messages to interception.
Abnormality detection
- You must be aware of any efforts to compromise your device or unusual network behavior. For you to determine if there was an employee error or a major threat, we transfer the pertinent connectivity information to your operational dashboards using the cloud communication platform from enmity.
Network-based firewall
- Small M2M devices typically have constrained computing power. They are unable to set up firewalls as a result. However, a network-based firewall safeguards your data as soon as it connects to the network. This prevents harmful data from ever being transmitted to the device or even being able to enter the network in the first place by removing the time-consuming task of packet filtering from the device.
Conclusion
- The Internet of Things (IoT) is a disruptive force that has the power to revolutionize whole sectors, improve the way we live our daily lives, and spur creativity in ways we never could have predicted. As linked devices continue to proliferate and the amount of data they produce grows exponentially, it is obvious that the Internet of Things (IoT) is not simply a fad but a core component of our increasingly digital world. IoT brings enormous benefits, but it also comes with several serious problems, such as interoperability issues, security and privacy concerns, and the need for strong regulatory frameworks. To guarantee that the advantages of IoT are fully realized while reducing the hazards, we must handle these difficulties.







